Private Network Reporter
Autonomous LAN security monitoring system built with Go, Nmap, and MikroTik RouterOS. Automatically discovers devices, scans them at configurable depth, and generates scheduled HTML security reports — all running as a single stateless binary inside a minimal Docker container.
Overview
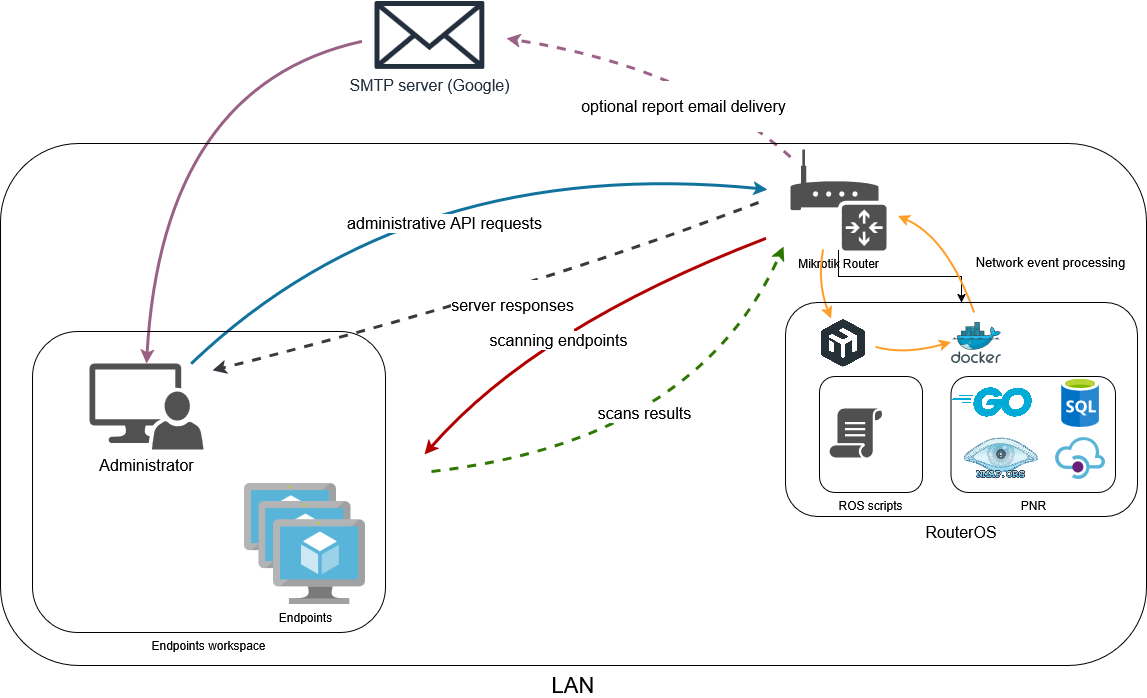
A lightweight, zero-dependency network security monitoring system designed for home and small-office networks that lack visibility into connected devices and exposed services. PNR automatically discovers devices through independent sources (e.g. DHCP events, Netwatch state changes, and ARP table harvesting), scans them with Nmap at configurable depth, and stores structured results in an embedded SQLite database. The system generates scheduled HTML security reports with sensitive-data detection and delivers them via email — all running as a single stateless binary inside a minimal Alpine Docker container. Integrates directly with MikroTik RouterOS (one of the most popular SOHO platforms) through event-driven webhook architecture with cryptographic authentication and replay attack prevention. Engineering thesis project demonstrating practical application of concurrent scan orchestration, dual-level cooldown protection, webhook-based RouterOS integration, and automated threat reporting. Perfect for security-conscious home users, small business networks, and anyone running MikroTik routers who needs continuous visibility into what's on their network.
Key Highlights
- ✓Three independent, extensible discovery sources: DHCP, Netwatch, and ARP harvesting
- ✓Concurrent worker pool (2–16) with dual-level per-MAC cooldown
- ✓Configurable scan depth: basic (60s), deep (300s), deepsafe, custom NSE script
- ✓SHA-512 webhook signatures with timestamp validation and replay protection
- ✓Scheduled HTML reports with NSE sensitive-script detection
- ✓Single stateless binary with embedded SQLite (WAL mode)
- ✓Auto-generated ECDSA certificates with TLS 1.2+ enforcement
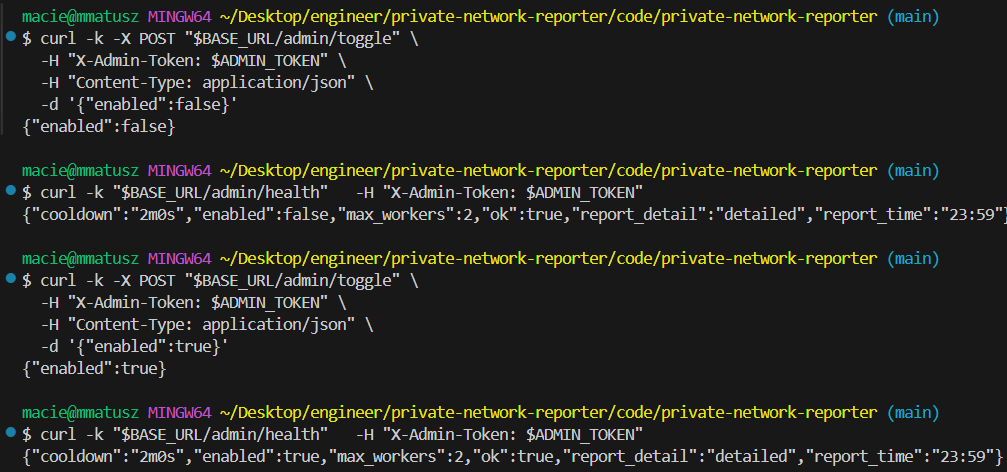
- ✓Admin REST API with constant-time token auth and rate limiting
Technical Deep Dive
System Architecture & Motivation
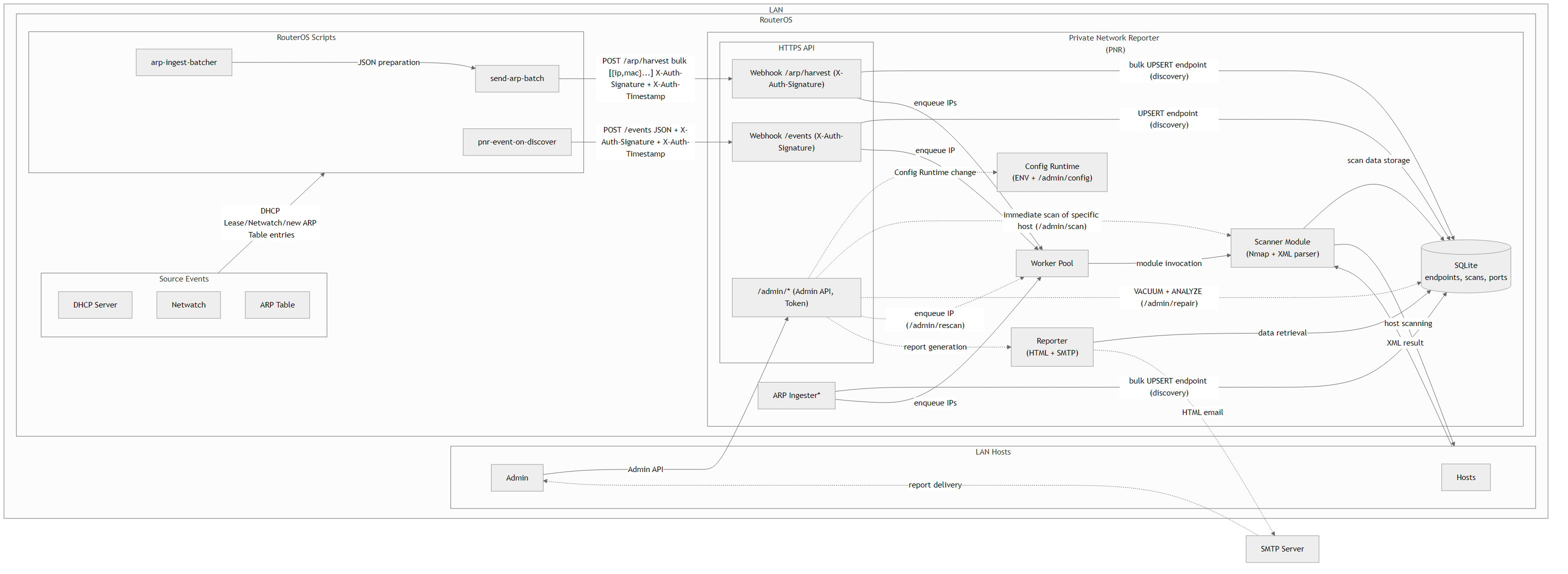
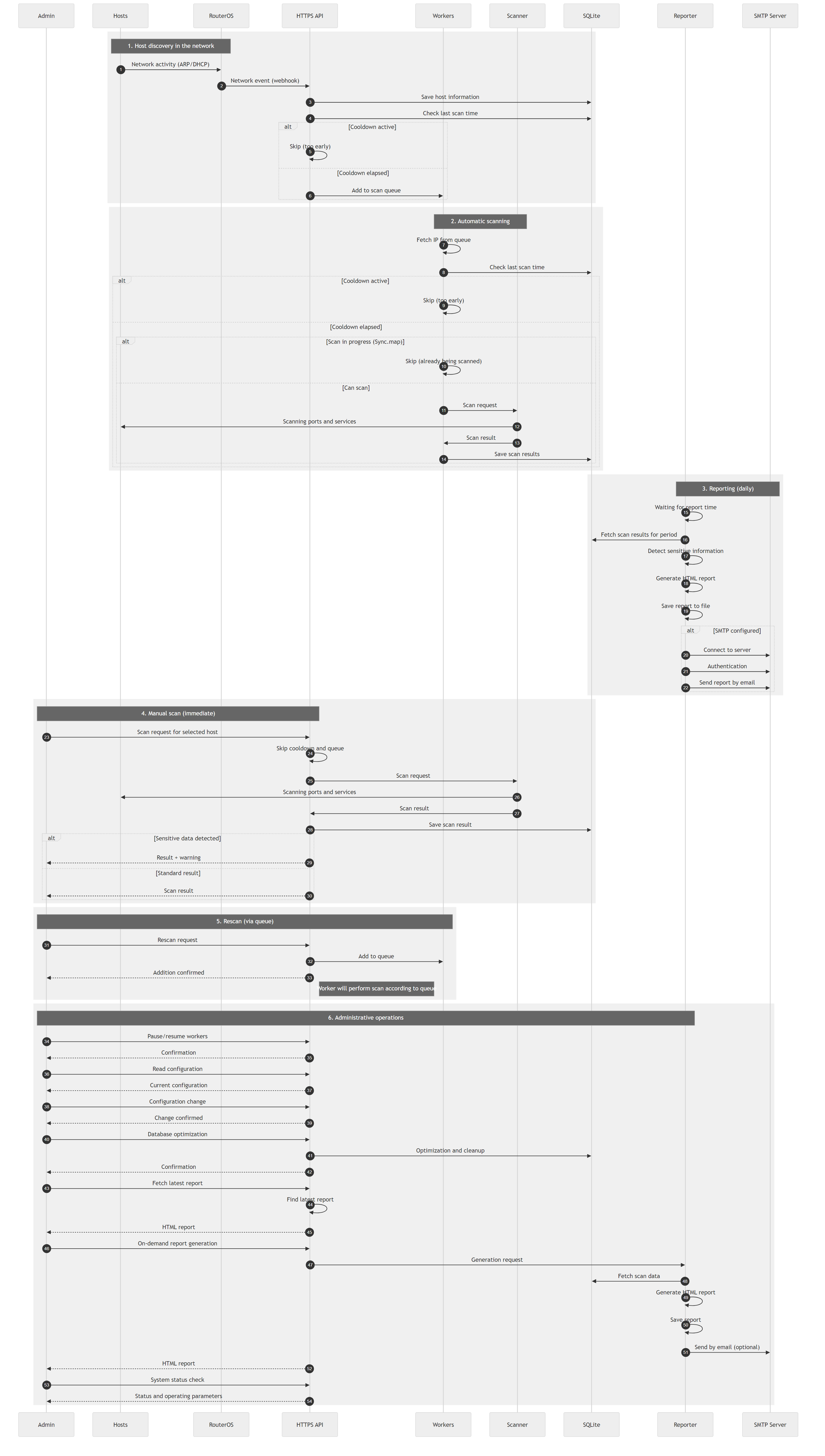
Home and small-office networks often lack visibility into what devices are connected and what services they expose. Enterprise-grade SIEM/NAC solutions are too complex and expensive for these environments. PNR fills that gap with a zero-dependency, self-contained monitoring system that plugs directly into MikroTik routers. The event-driven architecture processes DHCP lease and Netwatch webhooks from RouterOS, bulk ARP table pushes, and local /proc/net/arp monitoring (Linux container). All discovery events flow through a unified pipeline with MAC-based deduplication and cooldown protection before reaching the Nmap scanning workers.
Discovery & Scanning Pipeline
PNR discovers devices through three (extensible) independent channels: (1) DHCP lease webhooks triggered when a device joins the network, (2) Netwatch state change webhooks monitoring specific hosts, and (3) ARP table harvesting where RouterOS pushes the full ARP table in JSON batches every 2 minutes. Each discovery source feeds into a concurrent worker pool that executes Nmap scans. Dual-level cooldown protection (before queue insertion and inside the worker) prevents scan flooding based on MAC address, with IP fallback when MAC is unknown. Administrators can choose scan depth: basic (60s, port scan only), deep (300s with NSE scripts for detailed service detection), deepsafe (300s, safe NSE scripts only), or custom (custom time-window, chosen NSE scripts).
Security & Authentication
All webhooks from RouterOS are authenticated using SHA-512 HMAC: signature = SHA512(body + secret + timestamp). The system validates both the cryptographic signature and timestamp, rejecting requests older than 60 seconds or more than 30 seconds in the future. Per-source-IP replay protection tracks timestamps to prevent replay attacks. The Admin API is protected by X-Admin-Token header with constant-time comparison and per-IP token-bucket rate limiting. Transport security enforces TLS 1.2+ with auto-generated ECDSA P-256 certificates and modern cipher suites (ECDHE + AES-GCM / ChaCha20-Poly1305). Input validation includes IP address parsing, request body size limits (1 MB), and read/write/idle timeouts on the HTTP server.
Automated Reporting & Storage
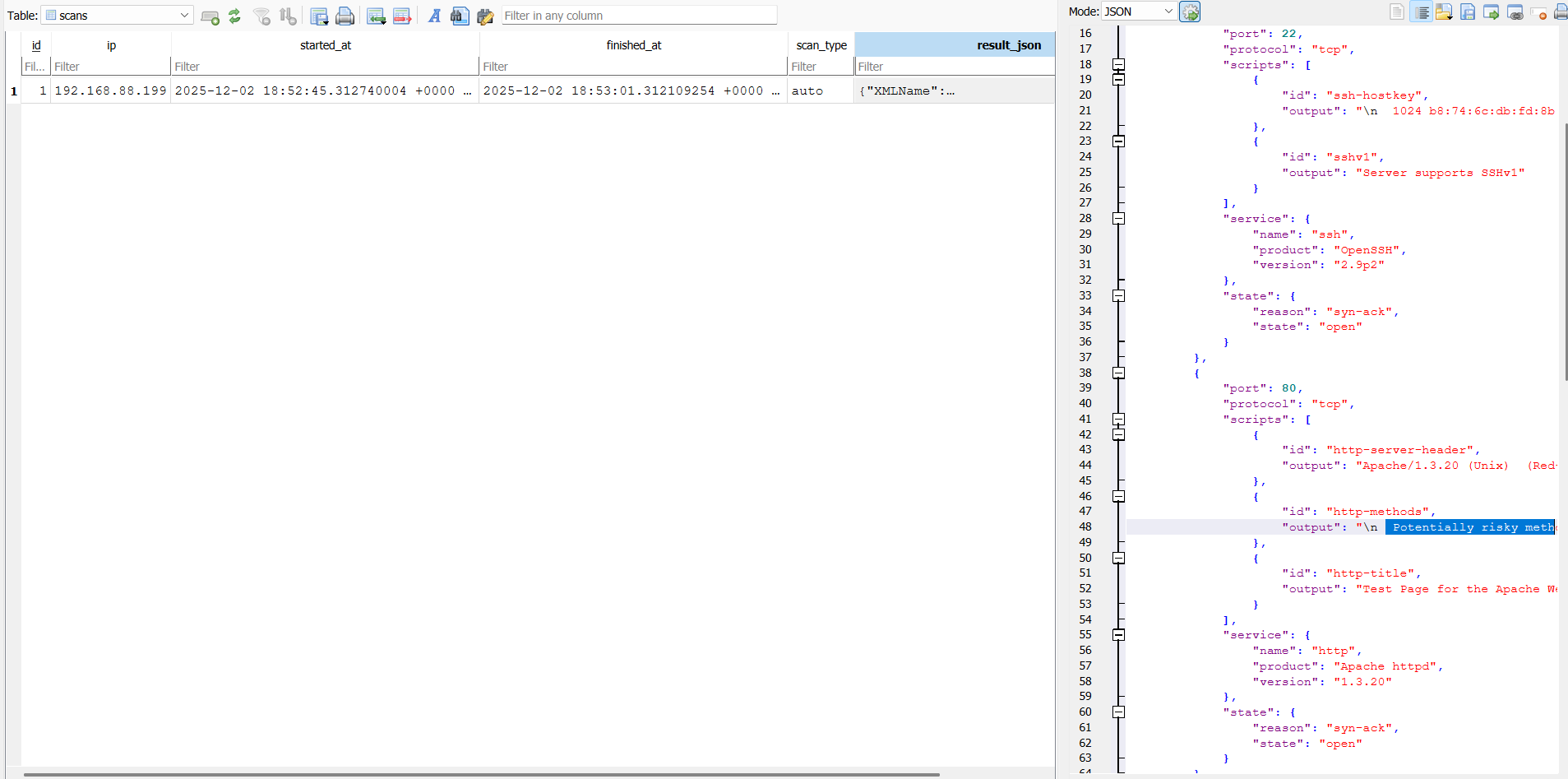
The system generates self-contained HTML reports scheduled daily at configurable time (default: 23:59) covering the last 24 hours. Reports include summary mode (host list with scan timestamps and open port counts) and detailed mode (additionally includes top-N open ports statistics across all scans). Sensitive script detection automatically flags scans containing NSE scripts that reveal potentially exploitable information (e.g., ssh-hostkey, ssl-cert, smb-os-discovery, ftp-anon). Reports are saved to /data/reports/ and optionally delivered via SMTP. All scan results are stored in embedded SQLite (WAL mode) with endpoints, scans, and ports tables. Full Nmap XML results are stored as JSON for deep analysis and forensics.
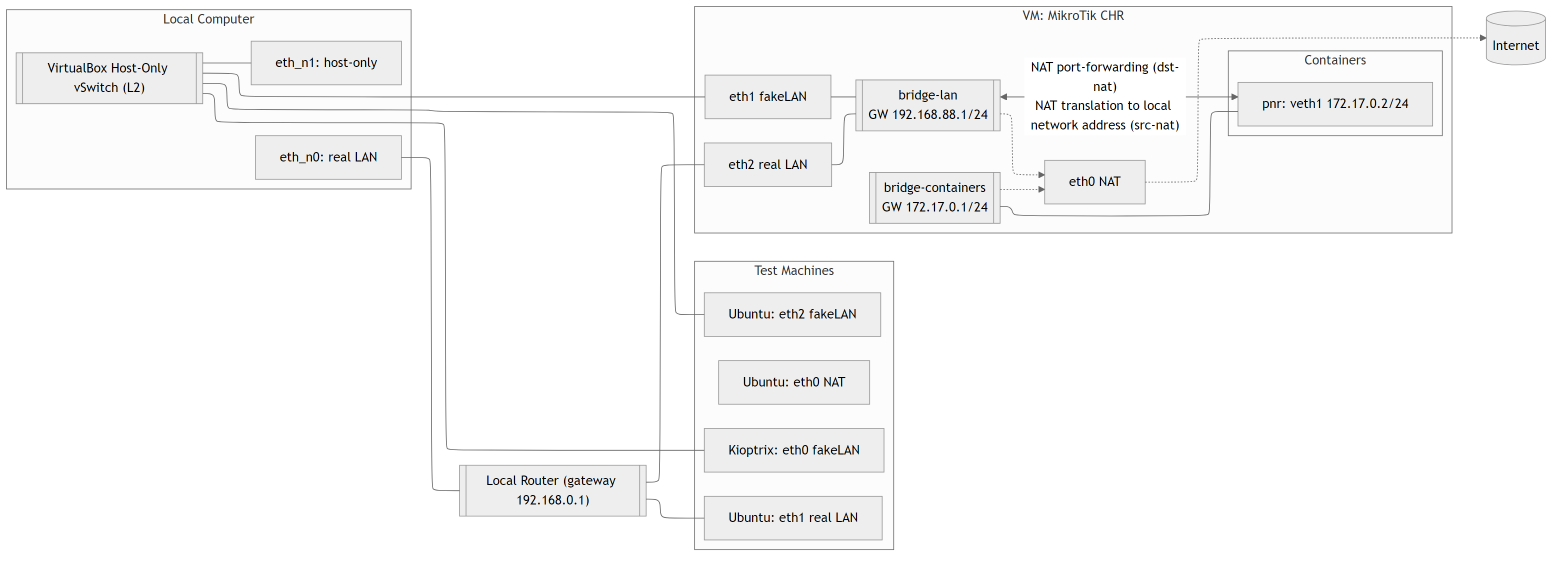
RouterOS Integration & Deployment
PNR ships with ready-to-use RouterOS scripts for seamless integration. The events.rsc script installs webhook handlers for DHCP leases and Netwatch, while arp-ingest-batcher collects and pushes the full ARP table every 2 minutes. Each event is cryptographically signed before transmission. The entire system runs as a single multi-stage Alpine Docker image with Nmap pre-installed and a persistent /data volume for database, certificates, and reports. Configuration is provided via environment variables or runtime Admin API calls. The stateless binary design makes it ideal for Docker Compose deployments, Kubernetes, or standalone VMs. Perfect for security professionals running MikroTik infrastructure who need continuous network visibility without enterprise SIEM complexity.