Plague: Advanced Malware Research
Academic research project demonstrating sophisticated malware techniques including adaptive attack strategies, multi-protocol lateral movement, and self-replication in controlled lab environments.
Overview
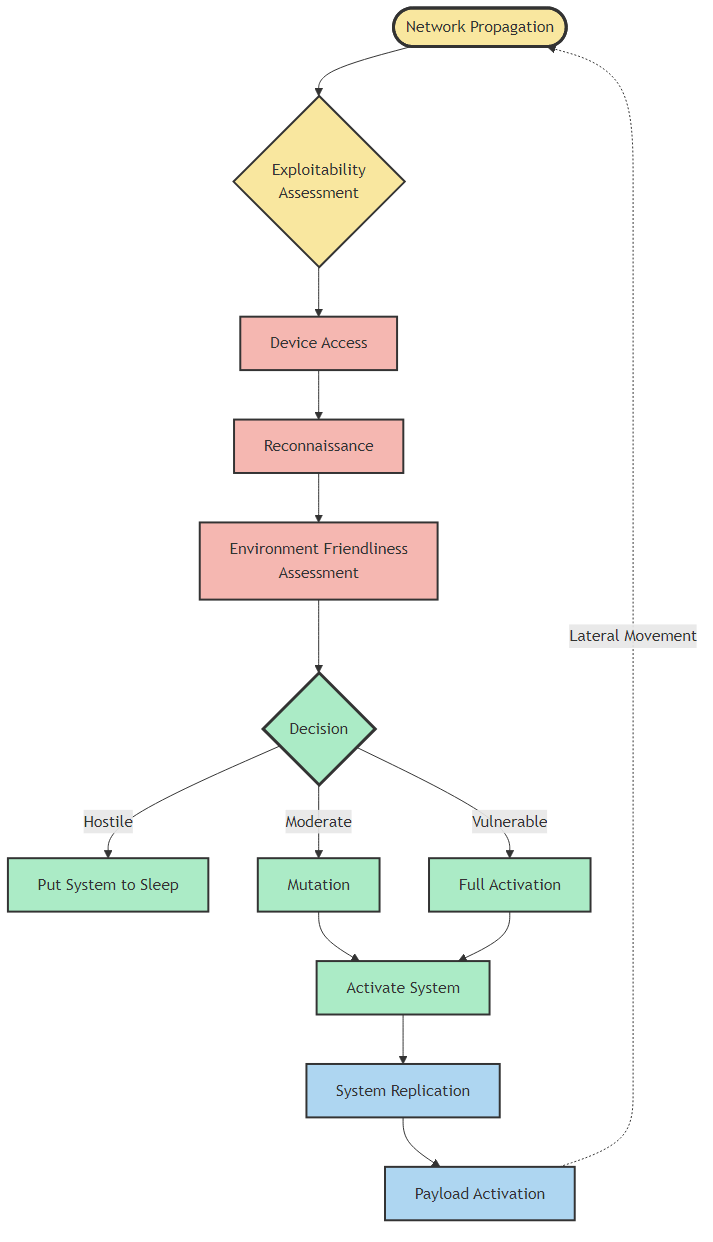
A comprehensive malware research platform developed for academic cybersecurity education, showcasing the complete attack kill chain from reconnaissance to impact. Features adaptive intelligence that evaluates system security posture and dynamically selects attack strategies (FullBlast, Moderate, HardToHack, StayLow, SilentMode). Implements advanced reconnaissance with vulnerability scanning (SUID files, writable /etc/passwd, kernel exploits), security tool detection (OSSEC, Wazuh, antivirus), and resource profiling. Demonstrates privilege escalation through cron job injection, automated log clearing, and ASLR bypass. Includes self-replicating capabilities with timestomping for stealth, and multi-protocol lateral movement across SSH, SMB, FTP, and HTTP. The C# ransomware payload showcases AES-256 file encryption. Deployed in isolated Vagrant + VirtualBox lab with 3 intentionally vulnerable Ubuntu VMs for safe testing. Integrated with GitLab CI/CD featuring SAST security scanning. FOR EDUCATIONAL AND DEFENSIVE RESEARCH ONLY.
Key Highlights
- ✓Adaptive attack strategy with 5 operational modes
- ✓Complete kill chain: reconnaissance → exploitation → persistence → lateral movement
- ✓Multi-protocol network propagation (SSH, SMB, FTP, HTTP)
- ✓Kernel & SUID vulnerability detection engine
- ✓Self-replication with timestomping stealth techniques
- ✓AES-256 ransomware payload in C#/.NET
- ✓Isolated Vagrant lab with intentionally vulnerable VMs
- ✓GitLab CI/CD integration with SAST security scanning
Technical Deep Dive
Reconnaissance & Intelligence
Automated system profiling detects OS, kernel version, virtualization status, SELinux configuration, and active security tools (antivirus, HIDS, logging services). Vulnerability scanning identifies SUID files, writable system files, vulnerable cron jobs, and known kernel exploits. Based on findings, the system evaluates security posture and selects an appropriate attack mode.
Multi-Stage Attack Chain
Demonstrates complete offensive security operations: (1) Reconnaissance phase profiles targets and identifies vulnerabilities, (2) Mutation phase exploits cron jobs for privilege escalation and creates persistent backdoor users, (3) Replication phase infects local Python/shell scripts with timestomping for stealth, (4) Lateral movement phase propagates across network via SSH, SMB, FTP, and CUPS protocols, (5) Impact phase deploys ransomware payload with AES-256 encryption.
Research Environment & Safety
Built for academic research with strict ethical guidelines. Vagrant-managed isolated lab environment with 3 Ubuntu VMs configured with intentionally weak security (open SSH, anonymous Samba shares, permissive FTP). Private network (192.168.56.0/24) ensures no external connectivity. GitLab CI pipeline includes SAST scanning to prevent accidental vulnerabilities. All code is professionally linted with Ruff and version-controlled with detailed commit history. Designed for defensive security education and malware analysis training.